This code hacks nearly every credit card machine in the country
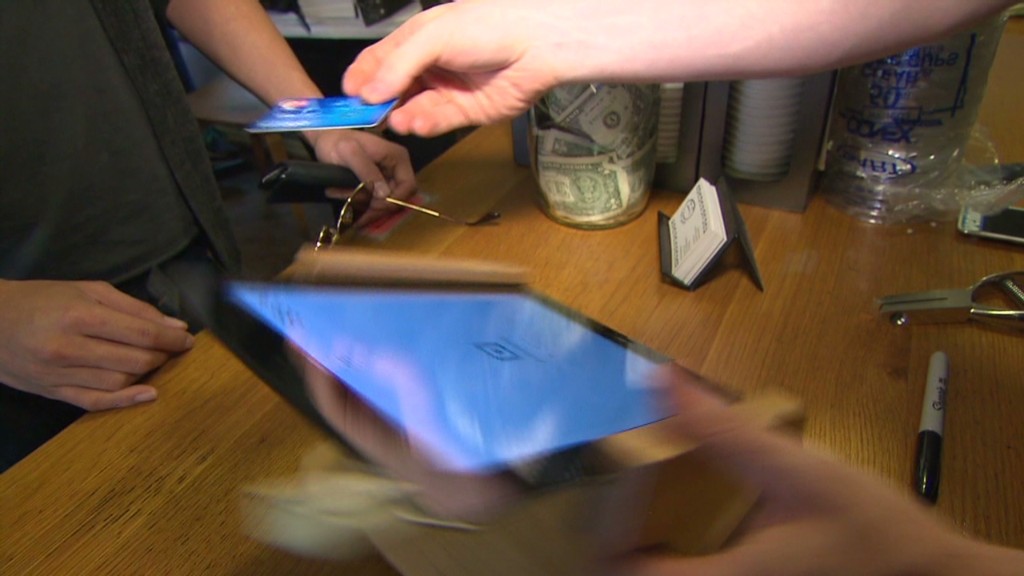
Get ready for a facepalm: 90% of credit rating card viewers at present use the exact same password.
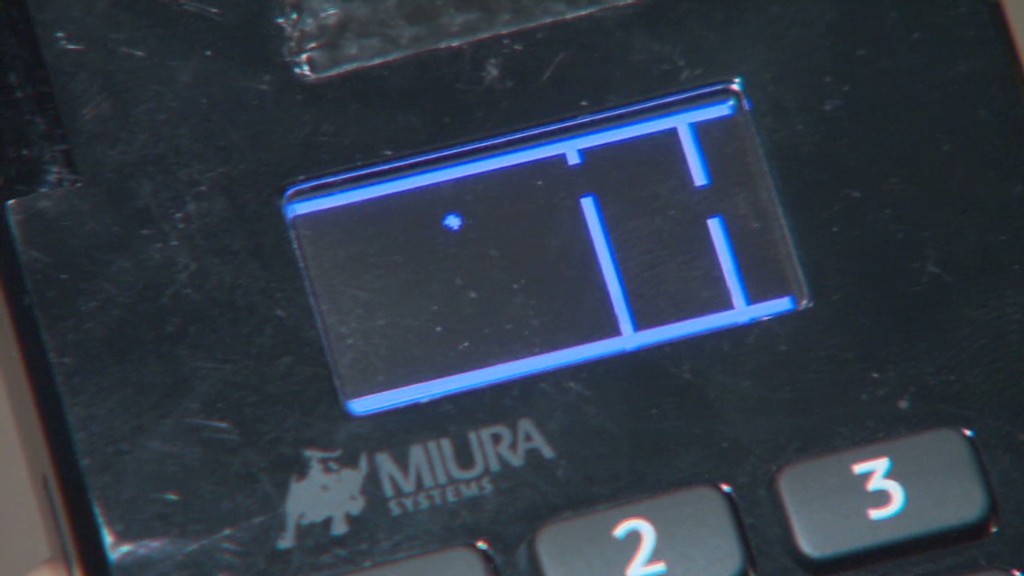
The passcode, set by default on credit rating card equipment considering that 1990, is easily observed with a speedy Google searach and has been exposed for so prolonged there is certainly no feeling in striving to disguise it. It can be either 166816 or Z66816, based on the equipment.
With that, an attacker can achieve finish command of a store’s credit card viewers, likely allowing for them to hack into the machines and steal customers’ payment data (assume the Concentrate on (TGT) and Home Depot (High definition) hacks all more than yet again). No marvel massive suppliers keep getting rid of your credit score card details to hackers. Protection is a joke.
This hottest discovery arrives from researchers at Trustwave, a cybersecurity agency.
Administrative access can be made use of to infect equipment with malware that steals credit history card info, described Trustwave govt Charles Henderson. He comprehensive his results at very last week’s RSA cybersecurity conference in San Francisco at a presentation called “That Stage of Sale is a PoS.”
Choose this CNN quiz — obtain out what hackers know about you
The issue stems from a activity of warm potato. Product makers promote equipment to special distributors. These sellers provide them to vendors. But no just one thinks it truly is their career to update the grasp code, Henderson advised CNNMoney.
“No a single is changing the password when they established this up for the initial time all people thinks the safety of their issue-of-sale is somebody else’s obligation,” Henderson said. “We are producing it really straightforward for criminals.”
Trustwave examined the credit score card terminals at more than 120 shops nationwide. That includes important apparel and electronics stores, as well as neighborhood retail chains. No distinct retailers were being named.
The vast majority of equipment had been created by Verifone (Fork out). But the very same situation is present for all important terminal makers, Trustwave claimed.

A spokesman for Verifone mentioned that a password on your own just isn’t enough to infect machines with malware. The enterprise reported, till now, it “has not witnessed any attacks on the safety of its terminals primarily based on default passwords.”
Just in case, although, Verifone mentioned suppliers are “strongly suggested to modify the default password.” And currently, new Verifone equipment arrive with a password that expires.
In any scenario, the fault lies with suppliers and their exclusive distributors. It can be like home Wi-Fi. If you purchase a household Wi-Fi router, it is up to you to adjust the default passcode. Vendors need to be securing their possess equipment. And equipment resellers need to be aiding them do it.
Trustwave, which can help protect vendors from hackers, explained that holding credit rating card devices safe and sound is low on a store’s record of priorities.
“Corporations expend a lot more income deciding on the coloration of the stage-of-sale than securing it,” Henderson explained.
This problem reinforces the conclusion designed in a recent Verizon cybersecurity report: that stores get hacked mainly because they’re lazy.
The default password point is a significant concern. Retail computer system networks get uncovered to pc viruses all the time. Contemplate just one case Henderson investigated lately. A terrible keystroke-logging spy computer software finished up on the pc a shop employs to system credit history card transactions. It turns out workers had rigged it to enjoy a pirated model of Guitar Hero, and unintentionally downloaded the malware.
“It demonstrates you the stage of access that a lot of people today have to the position-of-sale surroundings,” he mentioned. “Frankly, it truly is not as locked down as it must be.”
CNNMoney (San Francisco) 1st released April 29, 2015: 9:07 AM ET





